Detection Engineering Control Plane
Run a SOC that protects what matters.
Cover the threats that actually face your business. Benchmark your detection rules on day one. Let analysts triage real threats instead of drowning in noise.
Sound familiar?
Detection debt is burning out your SOC team
0 of 10. we solve all of them.
See how CraftedSignal helps →Start with risk, not alerts
Model business services and attack paths. Every MITRE technique gets weighted for your exposure. No more detections for threats you do not face, and no more blind spots for the ones you do.
Learn more →Catch silently broken rules
Industry data says only 5% of deployed detections actually work. We surface the dead ones the day they stop firing, plus noise, drift, failing tests, and missing mappings, in a single queue.
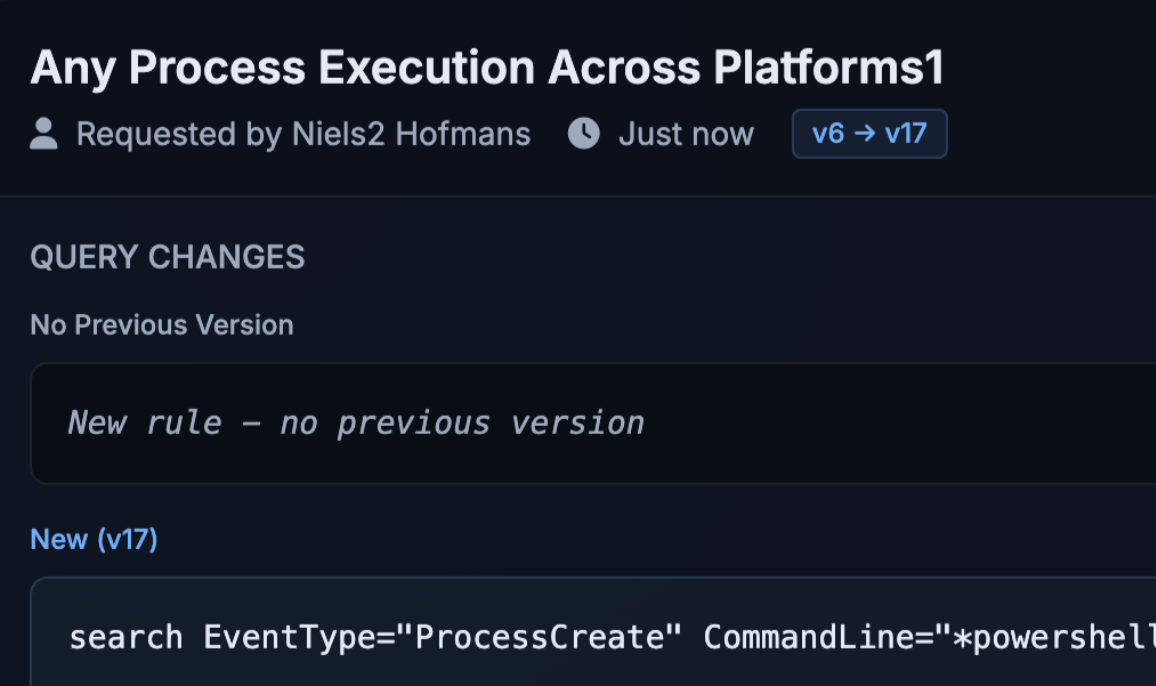
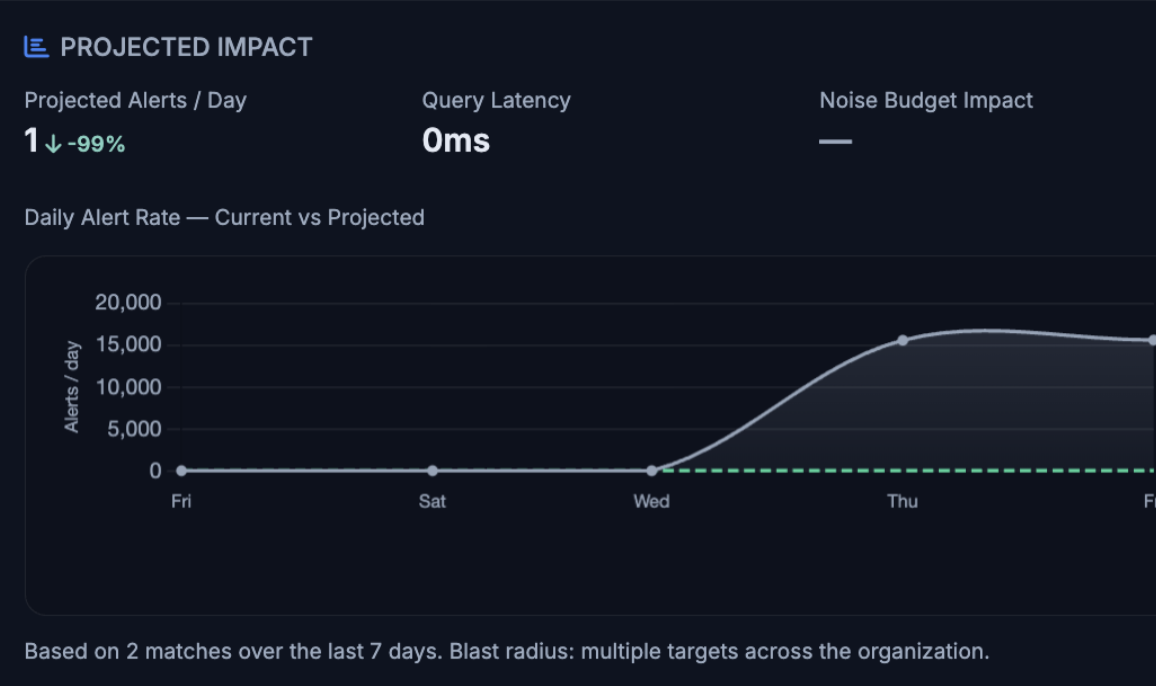
Learn more →Approve with impact preview
See the impact of every rule change before it hits your team. Juniors submit, seniors approve. Rollback in one click. Every action logged.
Learn more →Write Sigma, deploy everywhere
Author in Sigma and convert to Splunk, Sentinel, CrowdStrike, and Rapid7. Import native rules and translate to Sigma for portability, or keep writing in your SIEM's own language.
Learn more →Deploy safely, rollback instantly
Monitoring mode measures projected volume before alerting. Noise budgets block runaway rules. One-click rollback when things go wrong.
Learn more →Detections as Code
YAML rules in Git. Validate, test, and deploy with csctl or your CI/CD pipeline. Version history, diffs, and audit trail built in.
Learn more →Hunt, verdict, promote
Launch hypothesis-driven hunts against live SIEMs. Cluster results, verdict them in batch, and promote winning queries to tested Sigma rules in one click.
Learn more →Test live on your SIEM
Generate positive and negative test cases with AI, push them to your SIEM, and prove the rule fires (or doesn't) on real data, before a single alert reaches the analyst.
Learn more →AI you can unplug
Self-host Ollama or point at any OpenAI-compatible endpoint. Disable AI entirely if policy requires it. Every suggestion is logged, reviewable, and non-destructive by default.
Learn more →Threat intel that adopts itself
Receive signed threat briefs with Sigma rules, IOCs, and ATT&CK context. Relevance-scored against your industry. Adopt as rules, convert to hunts, or mark for monitoring, one click each.
Learn more →Catch drift before auditors do
Every deployed rule is re-hashed on a schedule. Any out-of-band change in the SIEM gets flagged, diffed, and queued for review. Separation of duties, proven automatically.
Learn more →Analyst feedback closes the loop
SOC analysts verdict alerts TP / FP / noise in the same UI. AI triages the feedback into concrete recommendations, tune this rule, retire that one, hunt this gap, ranked by impact.
Learn more →Noise budgets, enforced
Set a daily alert budget per team, per service, or per rule. Deploys that would blow the budget get held for review. Monitoring mode runs new rules silently until the volume proves out.
Learn more →Git-native backups
Every rule, every version, every test, pushed to your Git repo on a schedule. Restore from any point in history, audit offline, or migrate environments without touching the SIEM.
Learn more →SaaS, self-hosted, or air-gapped
One Go binary with an embedded Temporal, or fully managed SaaS. Regulated teams can run it air-gapped with outbound blocked. White-label branding for MSSPs and enterprise.
Learn more →How it works
From business risk to proven detection
Most detection tools start with a rule. We start with the risk the rule is supposed to protect, and we do not stop until coverage is proven, measured, and safe to retire.
Model the business
Declare your services, crown-jewel data, and attack paths. Industry profile and threat briefs weight every technique by actual risk to you.
Map the gaps
Every MITRE ATT&CK technique on your attack paths gets scored for exposure. See exactly which uncovered techniques matter, ranked by weight.
Prove the hypothesis
Launch a hunt against your live SIEMs. Cluster hits. Verdict them. Keep only what fires on real adversary behavior, and discard the noise.
Promote with confidence
Turn a winning hunt into a Sigma rule with tests, compile to every SIEM dialect, and deploy through impact preview + approval gates.
Prove, monitor, retire
Watch health and noise in real time. Catch silently broken rules the day they die. Feed results back into risk, and the loop closes.
Some visual examples
See the platform in action
Every screen below is real product. No mockups, no composited dashboards. This is what a SOC team uses on a Monday morning.
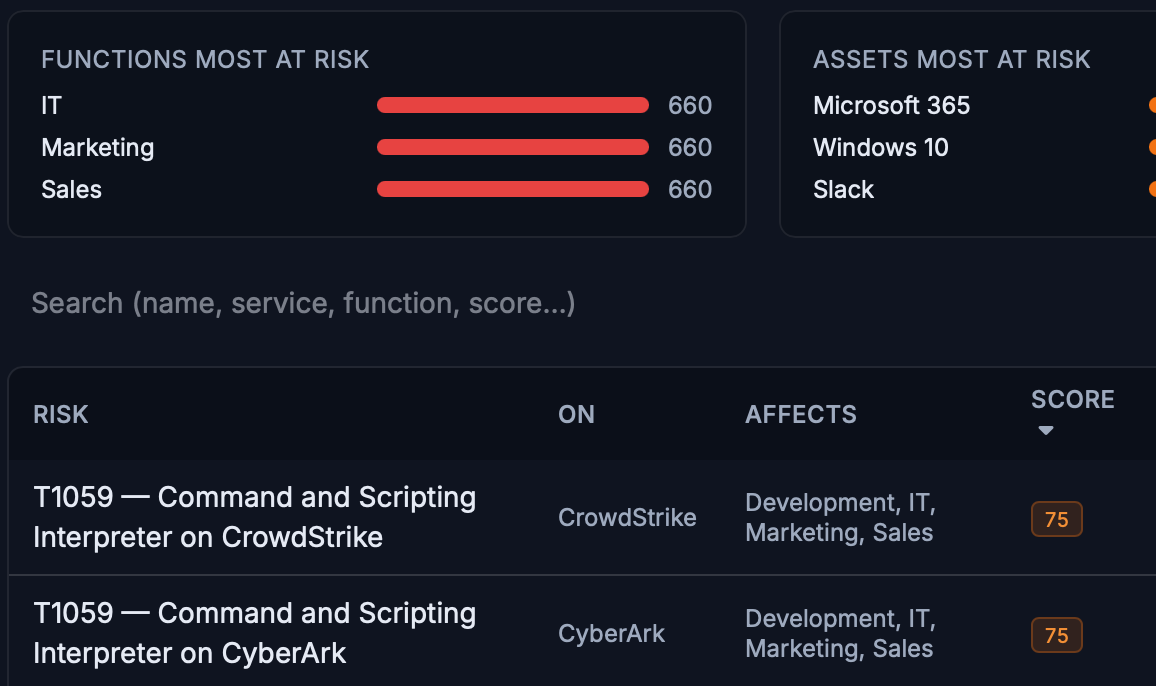
01 · Risk
One screen answers "are we covered?"
Exposure %, silently broken rules, SIEM health, and the top uncovered techniques with one-click Hunt / Rules actions.
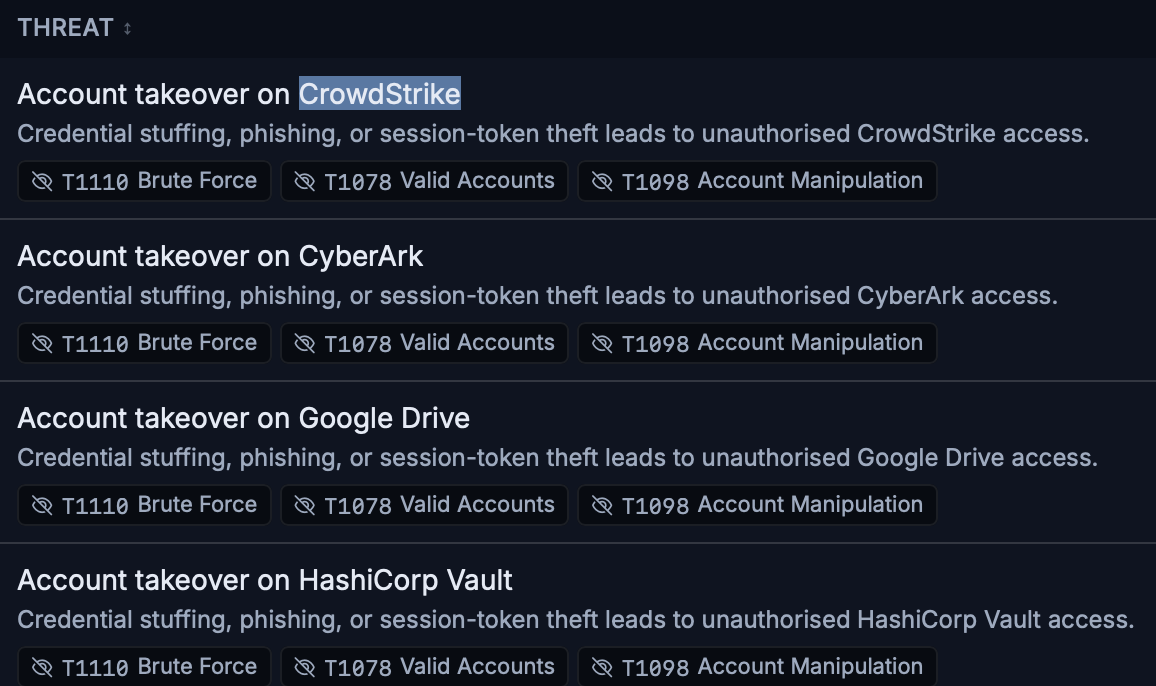
02 · Threat
Coverage depth, not just presence
Per-technique × per-layer heatmap (endpoint / network / identity / cloud / email). See where defense-in-depth is real and where it is paper-thin.
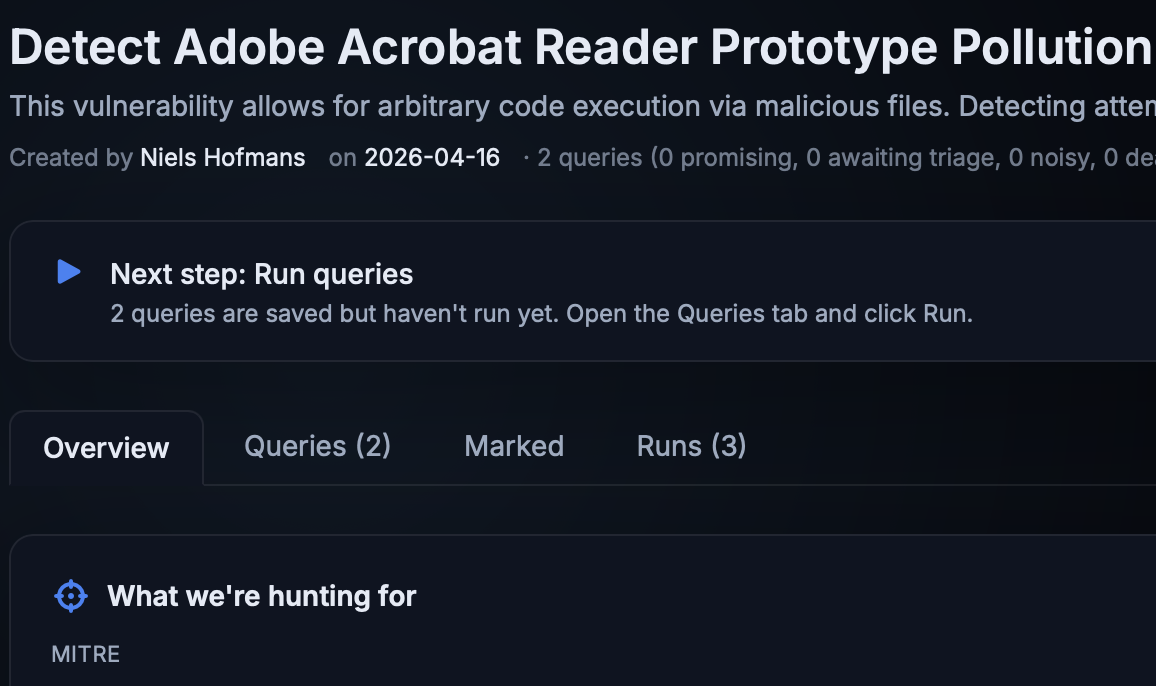
03 · Hunt
Cluster, verdict, promote
Hits grouped into clusters. One verdict covers dozens of rows. A promising query lands as a tested Sigma rule in a single click.
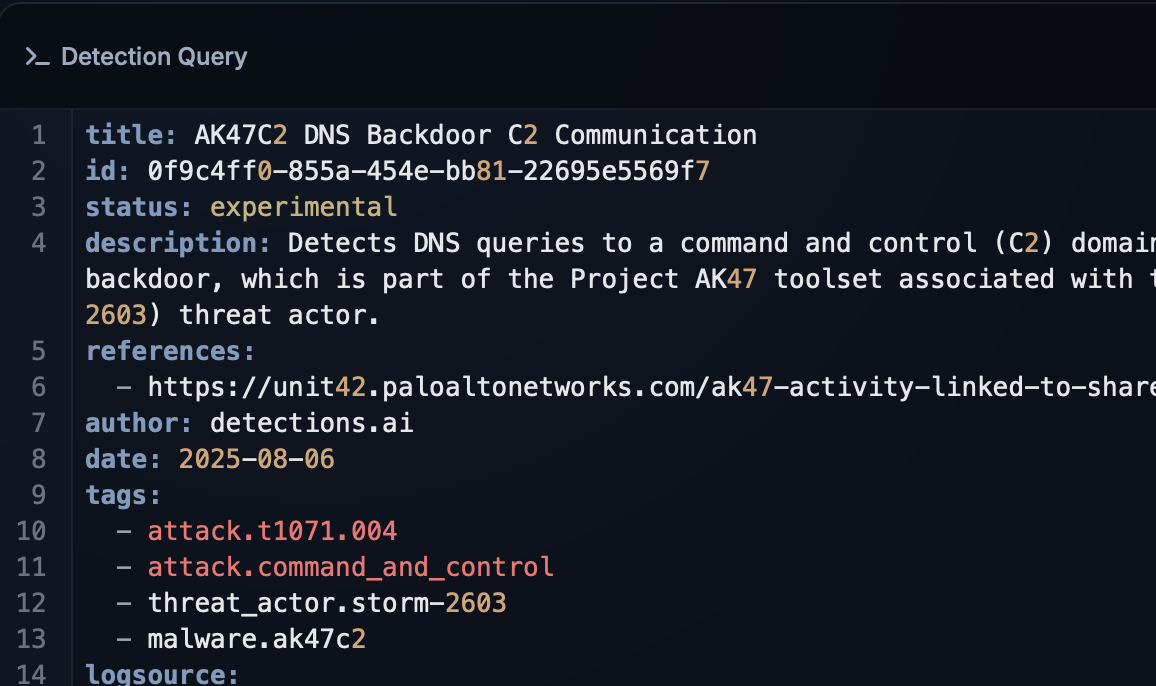
04 · Rule
Write Sigma to every SIEM at once
The rule editor compiles on every keystroke. Splunk SPL, Sentinel KQL, CrowdStrike FQL, Rapid7 LEQL — all visible side-by-side with unmapped-field warnings.
04 · Rule
Approve with full context
Before/after query diff. Projected alert volume. Critical-severity policy reminders. Comments are mandatory on rejection.
05 · Coverage
Catch the rules that stopped firing
A dedicated queue for rules deployed and active but producing zero triggers. Grouped by owning team so the right person hears about it first.
Enterprise-ready security
Built for security teams who can't compromise
AI on your terms
AI assists but never auto-deploys. Disable it entirely if your policy requires it. We never train on your data.
Batteries included
SSO, Passkey MFA, audit logs, RBAC, and approval workflows. Everything works out of the box.
SaaS or single binary
Use as SaaS or download a single binary. Generous free tier to try everything before you commit.
Feature toggles
Control every capability from the admin page. Override per-rule when teams need flexibility. The platform adapts to your security policy, not the other way around.